2. 山东鲁能软件技术有限公司, 济南 250001;
3. 中国石油大学(华东) 计算机科学与技术学院, 青岛 266580
2. Shandong Luneng Software Technology Co.Ltd, Jinan 250001, China;
3. College of Computer Science and Technology, China University of Petroleum, Qingdao 266580, China
在电力检修行业中施工行为是否规范关系到工作人员的人身安全, 对于电力行业的发展至关重要[1]. 人员行为分析是当前深度学习领域的一个重要的研究方向, 目前在电力行业的检修工作中已经基本实现了视频监控全覆盖, 通过对这些视频进行分析可以获得工作人员施工的相关信息. 针对电力检修工作人员的违规操作问题, 本文于从计算机视觉的角度对电力检修现场的违规行为进行检测, 基于Mask RCNN[2]计了一种多任务多分支违规行为检测网络, 综合目标检测、关键点检测与实例分割任务, 以获得违规行为检测所需的目标坐标、mask掩码与关键点信息. 同时为了避免实际应用中由于训练数据不足的过拟合问题, 设计了生成式数据增强与传统几何变换相结合的数据增强[3]策略来扩充数据集并通过交叉验证实验选取了最佳的超参数. 实验结果表明, 相对于原先的Mask RCNN, 基于改进Mask RCNN的电力维修违规检测方法具有更高的准确性和鲁棒性, 满足实际部署的精度要求.
2 相关工作自从Hinton等[4]在2012年提出深度学习的概念, 深度学习便逐渐取代了传统算法成为目标检测领域的主流方法. 到目前为止, 深度学习在图像处理领域已经取得了令人瞩目的成就. 近年来深度学习的发展为违规行为检测提供了新的方案, 卷积神经网络对于目标的几何变换、形变、光照等因素适应性较强, 有效克服了由于目标外观的多样性带来的识别阻力. 它可根据输入到网络的数据自动地生成相应特征的描述, 具有较高的灵活性和普适性[4,5]. 目前图像中的目标检测主要分为单步检测方法(如SSD, YOLO和CornerNet[6-8])和两步检测方法(如R-CNN、Fast R-CNN、Faster R-CNN[9-11]和Mask R-CNN[2])两种. 单步检测方法直接在图像上经过计算生成检测结果. 两步检测方法先在图像上提取候选区域, 再基于候选区域进行特征提取然后再进行预测. 单步检测算法的主要思想就是直接从输入图像得到目标物体的类别和具体位置, 不再像两步检测算法系列那样产生候选区域. 单步检测方法最显著的优势就是效率, 在检测精度上相对于两步检测方法则稍逊一筹.
语义分割是计算机视觉领域中的一个典型问题, 一般将其视作按照图像的语义来将图像进行分割, 即将图像中的每一个像素进行分类. 实例分割则比语义分割更进一步, 首先在图像中框出不同的实例, 然后再用语义分割的方法在不同的实例框中为每个区域的像素进行标记, 可将其视为目标检测与语义分割的结合体. FCN[12]是图像分割领域的里程碑式的突破, FCN全名为全卷积网络, 顾名思义, 即不包含全连接层的网络. FCN将CNN中的全连接层用1×1卷积代替, 可适应任意尺寸的输入, 并利用反卷积(DeConvolution)来实现对特征图的上采用, 最终得到具有较高准确性的分割图像. FCN实现了图像的端到端分割, 但是仍存在一定的缺陷, 如效率不够高、分割不够精细等. U-Net[13]是最近提出的应用于生物医学图像分割的卷积网络, 与FCN网络不同的是, U-Net的上采样阶段与下采样阶段采用了相同数量层次的卷积操作, 且使用skip connection结构将下采样层与上采样层相连, 使得下采样层提取道的特征可以直接传递到上采样层, 这使得U-Net网络的像素定位更加准确, 分割精度更高.
深度学习在关键点检测方向上的应用主要涉及人脸关键点检测以及用于姿态估计的人体关键点检测. Openface[14]是当前较为流行的一个人脸关键点检测框架, 基于Schroff等在CVPR2015上提出的Facenet[15], 该算法首先使用Dlib或者OpenCV检测到人的面部, 然后利用仿射变换使眼睛等标志点的位置固定, 具有较高的检测速度. CVPR2017上提出的PAF(Part Affinity Fields)[16]以一种自底向上的方式实现了在一整张图像中对其中的多人进行关键点检测. 该网络分为两大部分: 一部分根据特征图进行关键点预测; 另一部分获得每个关键点的PAF. 将这两部分进行联合学习和预测, 将这些关键点进行两两连接, 进而转化为图论问题.
何恺明在2017年提出的Mask RCNN是当前工业界最为流行的目标检测与分割框架之一, 既能准确检测出图像中的目标, 又能为一个目标生成具有较高质量的mask. Mask RCNN实际上是FasterRCNN的一个拓展, 相对于FasterRCNN, MaskRCNN做了如下改进:
1)用AoIAlign代替RoIPooling, 实现了特征图的像素级对齐;
2)在Faster RCNN每个RoI类标签和坐标两个输出的基础上添加了第三个Mask分支, 在每个RoI上利用FCN以pix2pix的方式实现Mask分割;
3) Mask分割分支易于向关键点检测分支拓展.
但是上述方法均为一个或者两个任务并行检测, 无法同时实现目标检测、实例分割和关键点检测任务, 在对人与物体有交互行为的电力检修违规检测问题上变得不再适用. 因此需要根据电力检修的实际需要, 结合现实中人与物体交互中的违规操作, 对Mask RCNN算法进行改进, 设计一种可以并行实现目标检测、实例分割与关键点检测的多任务多分支检测算法.
3 基于改进Mask RCNN的电力检修违规行为检测针对电力检修现场施工中的违规行为检测问题, 本文对Mask RCNN进行改进提出了一种多任务多分支的违规行为检测网络, 该方法在Mask RCNN的基础上将目标检测、关键点检测与实例分割在一个网络中整合, 实现了一种端到端的多任务检测算法; 同时, 将实例分割从目标检测分支中分离出来, 消除由目标检测边界框偏差带来的实例分割偏差; 对于分类误差、边框误差、实例分割误差和关键点检测误差, 设计了新的损失函数; 相对应用场景, 所得到的数据集偏少, 为避免实际应用中的过拟合问题, 设计了生成式数据增强与传统几何变换相结合的数据增强[3]策略来扩充数据集.
3.1 数据增强由于可以获得的数据集样本较少, 采用传统图像几何变换数据增强和利用GAN[17]进行生成式数据增强相结合的方法对数据集进行扩充. 对于传统的图像几何变换方法, 采用随机裁剪、水平翻转、图像倾斜、添加噪声、图像缩放和mixup[18]的方式对数据集进行了扩充, 图1为添加高斯噪声的图像.
|
图 1 添加高斯噪声图像示例 |
在用GAN对数据集进行扩充时, 采用DCGAN来生成新的图像[19]. DCGAN是比GAN拥有更多隐藏层的一种特殊GAN结构, 它与GAN在结构上的不同在于: 一是DCGAN中没有池化层(pooling层), 并且在生成器中使用转置卷积进行上采用而在判别器中使用微步幅卷积; 二是DCGAN去掉了全连接层从而使网络变成了全卷积网络, 这样的做法提高了输出图像的质量并且提高了模型的收敛速度.
如图2是本文采用的基于DCGAN的图像生成模型结构示意图. 其中生成器有15层, 判别器有16层, 在卷积层后使用了批归一化处理, 在生成器和判别器中均采用Leaky-ReLU作为激活函数.
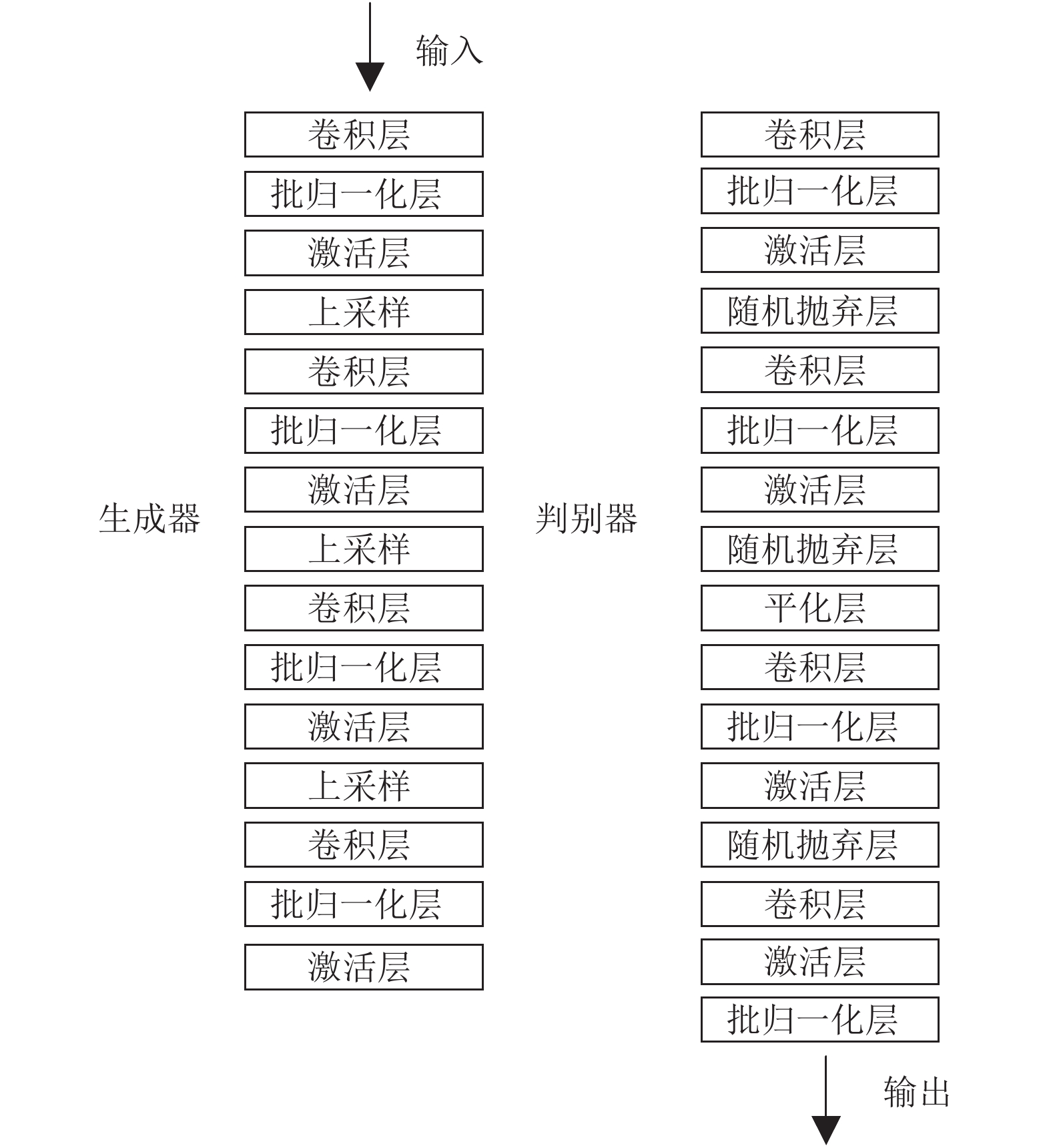
|
图 2 图像生成模型结构示意图 |
考虑计算机显存的限制, 在训练时统一将图像在800×600的尺寸上进行训练, 每16张图像为一个批次, 在生成器和判别器中均采用Adam作为优化器. 训练过程中生成的图像样本如图3所示.

|
图 3 生成图像示例 |
3.2 改进的Mask RCNN网络结构
经过改进的Mask RCNN实现了多个计算机视觉任务的并行处理, 该网络主要包括两个阶段: 第1阶段主要利用区域建议网络(RPN)生成可能存在目标的候选区域边界框; 在第2阶段中对第1阶段生成的每个候选区域利用RoIAlign进行对齐, 然后分别完成分类、边框回归、Mask预测及关键点预测.
如图4所示, 输入图像经过缩放以后输入特征提取骨架网络, 生成更具有更高阶特征的特征图, 以实现后面多个分支与RPN的特征共享. 在此选择的是ResNet101, 同时添加FPN以解决目标的多尺寸问题. 多个尺寸的特征图经过RPN生成多个无类别的候选区域, 并利用非极大值抑制(NMS)消除大量冗余候选区域, 这些候选区域经过RoIAlign在每一个分支上归一化成同一尺寸的特征图. 在RPN部分, 对于每一个三通道的图像中的每一个位置, 都会生成9个候选窗口: 3个纵横比{1:1,1:2,2:1}×3种尺寸{128,256,512}. 考虑到实际应用中瓷瓶、人体等目标的大小和比例, 对上述纵横比指标进行了相应的调整, 将原来的纵横比调整为{1:2,2:1,1:3,3:1}, 以此实现前景与背景的精准区分.
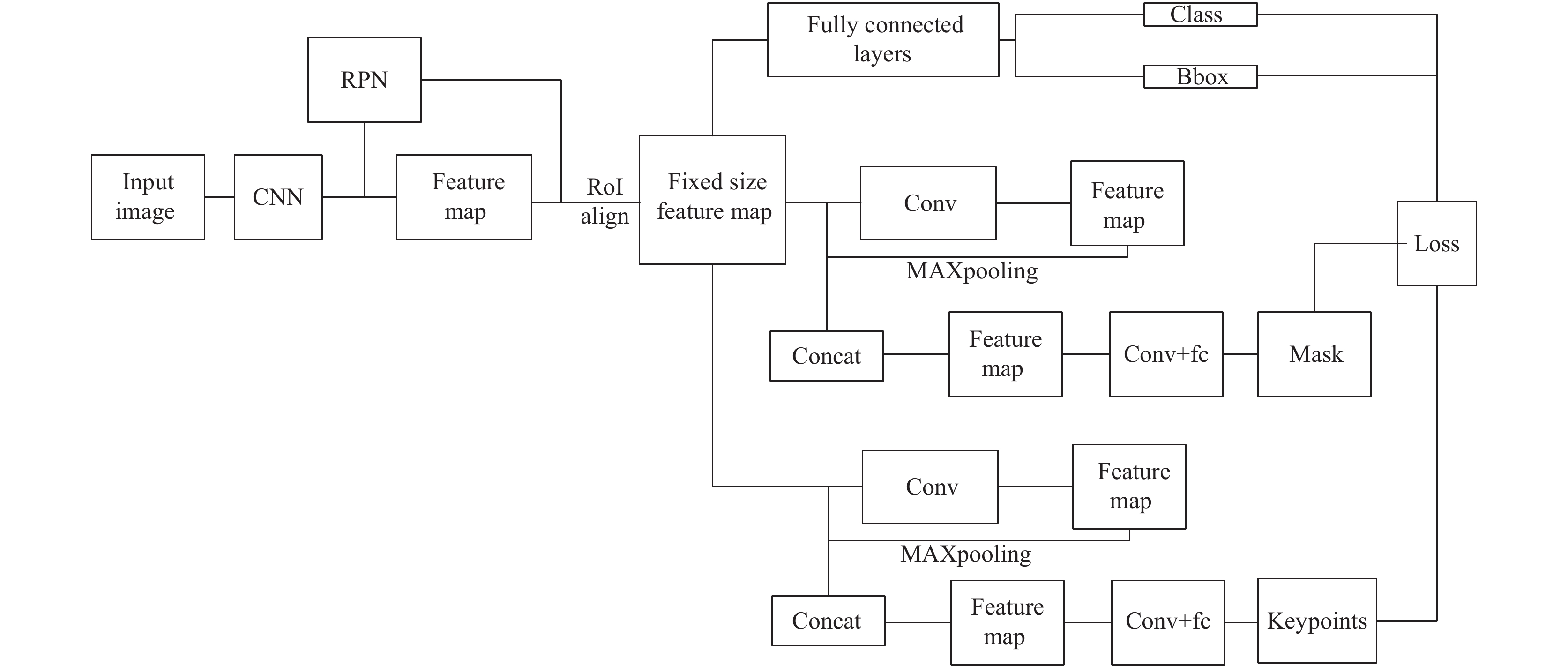
|
图 4 改进的Mask RCNN网络结构图 |
对于分类和边框回归, 经过归一化的特征图通过全连接层预测每个RoI的所属类别, 并对其坐标进行回归.
对于Mask预测, 与Mask RCNN不同的是, 在改进的Mask RCNN网络中Mask预测独立进行, 而不是依赖于目标的边框坐标, 以此消除由坐标偏差导致的实例分割误差. Mask预测分支将Mask预测分为两个部分, 类别预测和Mask回归, 由于在Mask类别预测上要与第一个分支一致, 在此可以直接引用第一个分支的类别信息而专注于Mask的回归. 因此需要对Mask的质量设计一个新的评估指标MaskIoU, 即真实Mask与预测Mask的交并比.
最后, 与Mask分支类似, 关键点检测分支在特征图上利用线性回归得到对应的预测位置.
3.3 损失函数设计对于各个分支中的各个任务而言, 其重要性是相同的, 但是在多任务学习中, 往往不同任务的学习难易程度不同, 若采用相同的损失权重, 会导致训练难以收敛. 如式(1), 针对各个任务, 分别设计独立的损失函数, 加权相加作为最终损失, 即损失=分类误差+坐标误差+分割误差+关键点误差, δ、ε、θ均为加权系数.
| $ Loss={L}_{\rm cls}+{\delta L}_{\rm bbox}+{\varepsilon L}_{\rm mask}+{\theta L}_{\rm kps} $ | (1) |
| $ {L_{\rm cls}} = \sum\nolimits_i {\left\{ { - {\rm{log}}\left[ {p_i^*{p_i} + \left( {1 - p_i^*} \right)\left( {1 - {p_i}} \right)} \right]} \right\}} $ | (2) |
目标坐标的损失函数如式(3)所示, 其中
| $ {L_{\rm bbox}} = \sum\nolimits_i {p_i^*} \left[ {\begin{array}{*{20}{c}} {{x_i}\log x_i^* + }\\ {{y_i}\log y_i^* + }\\ {\sqrt {{w_i}} \log \sqrt {w_i^*} + }\\ {\sqrt {{h_i}} \log \sqrt {h_i^*} + }\\ {\left( {1 - {x_i}} \right)\left( {1 - \log x_i^*} \right) + }\\ {\left( {1 - {y_i}} \right)\left( {1 - \log y_i^*} \right) + }\\ {\left( {1 - \sqrt {{w_i}} } \right)\left( {1 - \log \sqrt {w_i^*} } \right) + }\\ {\left( {1 - \sqrt {{h_i}} } \right)\left( {1 - \log \sqrt {h_i^*} } \right)} \end{array}} \right] $ | (3) |
Mask损失函数的设计主要侧重为: 将Mask划分至正确的类别, 并对前景对象类别的Mask进行回归. 但是在一个损失函数中难以同时实现两个功能, 并且Mask类别与目标分类分支的类别是一致的. 为了简化Mask类别损失可以直接取分类损失
| $ {L}_{\rm mask}={L}_{\rm cls}{*}MaskIoU $ | (4) |
其中,
| $ MaskIoU=\dfrac{{mask}_{\rm gt}\cap {mask}_{\rm pre}}{{mask}_{\rm gt}\cup {mask}_{\rm pre}} $ | (5) |
而关键点检测的损失函数则较为简单, 只需计算真实值与预测值之间的L1损失, 为了使损失函数更加平滑, 在此使用时SmoothL1作为关键点检测的损失函数.
| $ {L}_{\rm kps}={Smooth}_{L1}\left({kp}_{i}-{kp}_{i}^{*}\right) $ | (6) |
其中,
| $ Smoot{h_{L1}}\left( x \right) = \left\{ {\begin{array}{*{20}{c}} {0.5{x^2},\left| x \right| < 1}\\ {\left| x \right| - 0.5,\left| x \right| > 1} \end{array}} \right.$ | (7) |
本次实验以检测人员在瓷瓶上挂安全带为例, 训练集图像共有3000张, 通过数据增强将训练集扩充至20 000张. 在模型训练与测试时采取的是10折交叉验证的方式, 即将数据均分为10份, 每次训练集取其中9份, 留1份作为测试集, 最终结果为10次平均值.
实验显卡配置NVIDIA GeForce GTX TITAN X, 处理器为Intel i7.
在本实验中, 以目标检测任务为例. 首先, 我们要先对所有的检测结果排序, 得分越高的排序越靠前, 然后依次判断检测是否成功. 将排序后的所有结果定义为DTs (预测框), 所有同类别的真实目标定义为GTs(真实框). 先依序遍历一遍DTs中的所有DT, 每个DT和全部GT都计算一个IoU (bbox的交并比), 作为检测任务性能的评价指标, 如果最大的IOU超过了给定的阈值, 那么视为检测成功, 算作TP (True Positive); 如果该DT与所有GT的IOU都没超过阈值, 自然就是FP (False Positive). 同理, 实例分割及关键点检测任务性能的评价与目标检测类似.
实验过程中, 对于目标检测、实例分割、关键点检测分别有各自的评价指标, 并分别设置了相对应的阈值, 具体指标如表1所示.
| 表 1 评价指标 |
4.1 改进的MaskRCNN效果测试
如图5为Mask RCNN检测算法测试效果图, 从图中可以看出, 在此场景下存在人员漏检的情况.

|
图 5 Mask RCNN检测算法测试效果图 |
图6为改进的Mask RCNN多任务检测算法测试效果图. 从图中可以看出, 使用改进后的Mask RCNN多任务检测算法可以更为准确地检测出相关目标信息, 综合了目标检测、关键点检测与实例分割任务, 并且可以通过施加额外的判断逻辑对瓷瓶上挂安全带这一违规行为准确检测. 其中红框为瓷瓶上安全带的检测结果, 蓝框则表示存在人员在瓷瓶上挂安全带的违规行为. 表2为检测效果对比.
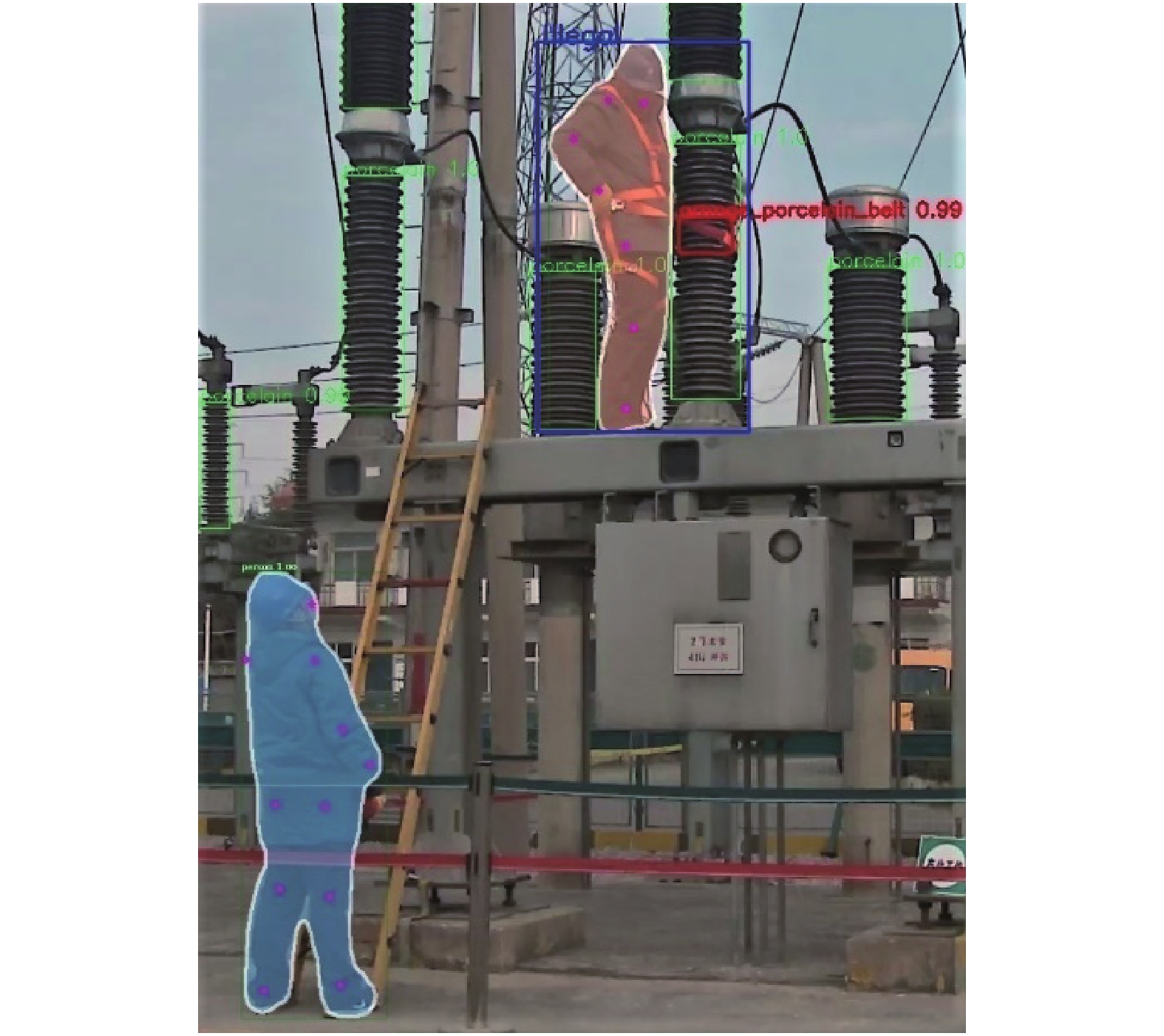
|
图 6 改进的Mask RCNN多任务检测算法测试效果图 |
| 表 2 改进的Mask RCNN与Mask RCNN检测效果对比 |
4.2 测试超参数选择
在模型测试时, 发现电力检修现场中由于遮挡或者各种检修设备的干扰, 存在一定的误检或者将一个目标检测为两个的现象. 为了解决此类问题, 可以采用NMS的方法对检测到的冗余目标进行消除, 不同的NMS数值与准确率(Precision)、召回率(Recall)的关系如表3所示中准确率和召回率有如下定义, 其中TP代表检测正确的结果数量, FN表示漏检的数量, FP表示误检测结果数量.
| $ Precision=\dfrac{TP}{TP+FP} $ | (8) |
| $ Recall=\dfrac{TP}{TP+FN} $ | (9) |
从表中可以看出, 随着NMS的递增, 误检逐步增加, 而漏检逐步递减. 原因在于NMS越小, 两个检测框交并比在较小的时候就视为同一个目标, 这样就会尽可能地消除冗余框. 经过对准确率和召回率进行权衡, 最终在实际应用中选择0.4作为NMS值.
4.3 数据增强为了测试该方法所采用的数据增强技术对准确率的影响, 对无数据增强、传统的图像几何变换、GAN、GAN与图形变换相结合的方式进行了对照实验, 其中原始图像3000张, 传统的图像几何变换生成新的图像7000张, GAN生成新图像10 000张. 实验结果如表4所示, 可以看出, GAN与传统图像几何变换相结合的方式可以极大地提高模型的准确率.
| 表 3 NMS对测试结果影响(%) |
| 表 4 对照实验(%) |
5 结论与展望
针对电力检修工作中的违规行为检测问题, 本文对Mask RCNN算法进行了改进, 主要贡献包括实现了目标检测、实例分割、关键点检测的多任务端到端检测; 将实例分割分支与目标检测分支相分离, 避免由于目标检测分支误差给实例分割带来的负面影响; 针对数据集不足的问题采用多种方式进行数据扩充; 结合实际应用情况, 利用交叉验证选取了最优的NMS超参数. 实验结果表明, 相对于原来的Mask RCNN, 该算法在准确性上有了显著的提升, 具有更高的准确性和鲁棒性, 在电力检修违规检测方面满足实际部署的精度要求. 在未来还将考虑将人与物体的交互赋予可学习的判断逻辑, 实现端到端的违规操作检测.
| [1] |
刘洋. 略论电力施工和检修的安全控制策略. 河南科技, 2015(22): 193. DOI:10.3969/j.issn.1003-5168.2015.22.155 |
| [2] |
He KM, Gkioxari G, Dollár P, et al. Mask R-CNN. Proceedings of 2017 IEEE International Conference on Computer Vision. Venice, Italy. 2017. 2980–2988.
|
| [3] |
Lamburt L, Koyfman L. Data enhancement techniques: USA, 6397228. 2002-05-28.
|
| [4] |
Krizhevsky A, Sutskever I, Hinton GE. Imagenet classification with deep convolutional neural networks. Proceedings of the 25th International Conference on Neural Information Processing Systems. Lake Tahoe, NV, USA. 2012. 1097–1105.
|
| [5] |
LeCun Y, Bengio Y, Hinton G. Deep learning. Nature, 2015, 521(7553): 436-444. DOI:10.1038/nature14539 |
| [6] |
Liu W, Anguelov D, Erhan D, et al. SSD: Single shot multibox detector. Proceedings of the 14th European Conference on Computer Vision. Amsterdam, the Netherlands. 2016. 21–37.
|
| [7] |
Redmon J, Divvala S, Girshick R, et al. You only look once: Unified, real-time object detection. Proceedings of 2016 IEEE Conference on Computer Vision and Pattern Recognition. Las Vegas, NV, USA. 2016. 779–788.
|
| [8] |
Law H, Deng J. Cornernet: Detecting objects as paired keypoints. Proceedings of the 15th European Conference on Computer Vision. Munich, Germany. 2018. 765–781.
|
| [9] |
Girshick R, Donahue J, Darrell T, et al. Rich feature hierarchies for accurate object detection and semantic segmentation. Proceedings of 2014 IEEE Conference on Computer Vision and Pattern Recognition. Columbus, OH, USA. 2014. 580–587.
|
| [10] |
Girshick R. Fast R-CNN. Proceedings of 2015 IEEE International Conference on Computer Vision. Santiago, Chile. 2015. 1440–1448.
|
| [11] |
Ren SQ, He KM, Girshick R, et al. Faster R-CNN: Towards real-time object detection with region proposal networks. Proceedings of Advances in Neural Information Processing Systems. Montreal, QB, Canada. 2015. 91–99.
|
| [12] |
Long J, Shelhamer E, Darrell T. Fully convolutional networks for semantic segmentation. Proceedings of 2015 IEEE Conference on Computer Vision and Pattern Recognition. Boston, MA, USA. 2015. 3431–3440.
|
| [13] |
Ronneberger O, Fischer P, Brox T. U-net: Convolutional networks for biomedical image segmentation. Proceedings of the 18th International Conference on Medical Image Computing and Computer-Assisted Intervention. Munich, Germany. 2015. 234–241.
|
| [14] |
Amos B, Ludwiczuk B, Satyanarayanan M. OpenFace: A general-purpose face recognition library with mobile applications. Pittsburgh: Carnegie Mellon University, 2016. 6.
|
| [15] |
Schroff F, Kalenichenko D, Philbin J. Facenet: A unified embedding for face recognition and clustering. Proceedings of 2015 IEEE Conference on Computer Vision and Pattern Recognition. Boston, MA, USA. 2015. 815–823.
|
| [16] |
Cao Z, Simon T, Wei SE, et al. Realtime multi-person 2D pose estimation using part affinity fields. Proceedings of 2017 IEEE Conference on Computer Vision and Pattern Recognition. Honolulu, HI, USA. 2017. 1302–1310.
|
| [17] |
Goodfellow IJ, Pouget-Abadie J, Mirza M, et al. Generative adversarial nets. Proceedings of the 27th International Conference on Neural Information Processing Systems. Cambridge, UK. 2014. 2672–2680.
|
| [18] |
Zhang HY, Cisse M, Dauphin YN, et al. Mixup: Beyond empirical risk minimization. arXiv: 1710.09412, 2017.
|
| [19] |
Radford A, Metz L, Chintala S. Unsupervised representation learning with deep convolutional generative adversarial networks. arXiv: 1511.06434, 2015.
|
 2020, Vol. 29
2020, Vol. 29


